Prism Oracle
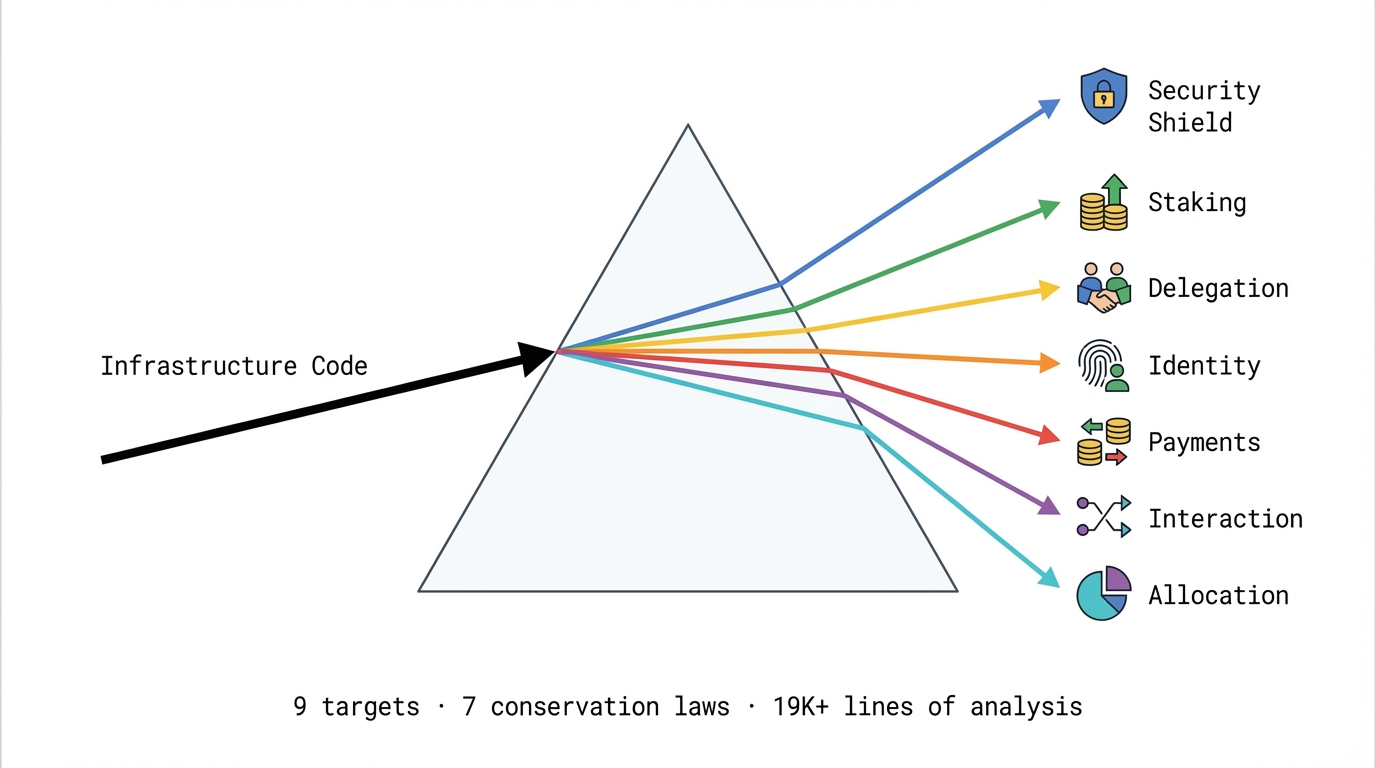
A cognitive prism is a 332-word prompt that changes how AI models frame problems. Instead of code review, the model produces conservation laws — structural trade-offs that predict where future vulnerabilities will appear. We analyzed 9 infrastructure targets the Ethereum ecosystem depends on.
9
Targets Analyzed
7
Conservation Laws
19K+
Lines of Analysis
OpenZeppelin — Security Bedrock of Ethereum
ERC20, Ownable, AccessControl, ReentrancyGuard. 738 lines source.
Conservation Law
Safety × Gas Efficiency × Social Flexibility = Constant
5
Composition Hazards
2,539
Lines of Analysis
10
Pipeline Passes
Role State Synchronization Paradox
Owner grants admin role, renounces ownership, keeps admin — orphaned privileges no component detects.
Exploit Surface
permit() bypasses standard allowance checks. Transitive permission escalation via grantRole(). Admin hierarchy bypass through contract-to-contract role grants.
Lido stETH — Liquid Staking Infrastructure
StETH + Lido core. 1,905 lines source.
Conservation Law
Observer-Dependent Value × Denomination = Constant
3
Exploit Vectors
3,508
Lines of Analysis
10
Pipeline Passes
Observer-Dependent Value Creation
The share rate isn't hiding a true value — it creates value by being different for each observer.
Exploit Surface
Dilution attacks via adapters minting unbacked shares. Front-running via oracle information asymmetry. Staking router loads withdrawal queues without allowlist.
MetaMask Delegation Framework
DelegationManager, DeleGatorCore, CaveatEnforcer. 971 lines source.
Conservation Law
Temporal Consistency × Computational Composability = Constant
3
Exploit Vectors
2,271
Lines of Analysis
9
Pipeline Passes
Permission Amplification
A delegates to B, B delegates to C — C executes as A without A's authorization. Independent deployment guarantees coordination failures at boundaries.
ERC-8004 — The Hackathon's Own Infrastructure
Identity + Reputation + Validation registries. 549 lines source.
Conservation Law
Information Access × Execution Efficiency = Constant
7
Findings
2,665
Lines of Analysis
10
Pipeline Passes
Identity Fragmentation
Phantom identities through normalization inconsistency. ENS domain seizure permanently breaks agent identity. Circular delegation creates infinite loops (DoS via gas exhaustion).
x402 Protocol — Coinbase Payment Infrastructure
Client + server + facilitator core. 2,026 lines source.
Conservation Law
Deployment Decoupling ↔ Operational Coherence
5
Findings
2,908
Lines of Analysis
10
Pipeline Passes
Centralized Assumptions in Distributed Protocol
Facilitator is single point of trust in a protocol designed to minimize trust. Race conditions in async hook state. Silent failures when networks overlap.
Octant — Public Goods Allocation
Epochs, Deposits, Proposals, Vault, Auth. 560 lines source.
Conservation Law
Historical Fidelity × Computational Directness × Config Flexibility = Constant
5
Contracts Analyzed
2,440
Lines of Analysis
10
Pipeline Passes
Epoch Allocation Impossibility
Cannot simultaneously maintain historical records, compute allocations efficiently, and allow flexible configuration changes.
ERC-8183 — Agent Interaction Standard (Virtuals)
The agent-to-agent interaction spec. 730 lines source.
Conservation Law
Decision Centralization × Temporal Efficiency = Constant
7 HIGH + 3 MED
Bugs Found
2,595
Lines of Analysis
10
Pipeline Passes
7 HIGH-Severity Fixable Bugs
setBudget authorization missing, expectedBudget field absent, meta-transactions broken, hook liveness unguarded. Budget negotiation deadlock. Evaluator fee incentive distortion.
Framework Validations
Methodology transfers beyond Ethereum — same prisms produce conservation laws on any structured codebase.
Conservation Law
Complexity cannot be eliminated, only relocated between layers
high
Recursive mount — stack overflow
high
redirect_slashes — infinite redirect
Conservation Law
Context isolation trades against ergonomics
high
Chain mode — args leak between commands
high
Shallow copy — nested dicts shared across contexts
Try It — Analyze Any Input
Opus ~$0.50 · Sonnet ~$0.06 · Haiku ~$0.02
Analyzing...
Results
Depth
Cost
Bugs
Confidence